Modern civilization depends on invisible digital systems. Electricity grids, nuclear power plants, transportation networks, hospitals, water treatment facilities, and industrial factories increasingly rely on computers and internet-connected technologies. While this improves efficiency and automation, it also creates dangerous vulnerabilities.
Today, cyberattacks are no longer limited to stealing passwords or damaging websites. Governments and cybersecurity experts warn that cyber weapons can target entire infrastructures capable of affecting millions of people.
Attacks on power stations, pipelines, and water systems demonstrate that digital warfare has become one of the most serious security challenges of the 21st century.
What Is a Cyber Weapon?
A cyber weapon is malicious software or a digital system designed to:
- Disrupt operations
- Damage infrastructure
- Steal critical information
- Manipulate industrial systems
Unlike ordinary cybercrime, cyber weapons are often associated with:
- State-sponsored operations
- Military conflicts
- Strategic sabotage
Some attacks are designed not simply to steal data, but to physically affect real-world systems.
Why Critical Infrastructure Is Vulnerable
Modern infrastructure increasingly uses industrial computer systems connected through networks.
Examples include:
- Nuclear plants
- Water treatment facilities
- Electrical grids
- Gas pipelines
- Transportation systems
Many of these systems were originally designed decades ago before cybersecurity became a major concern.
As a result, some infrastructure networks still rely on:
- Outdated software
- Weak security practices
- Poor network isolation
This creates opportunities for attackers.
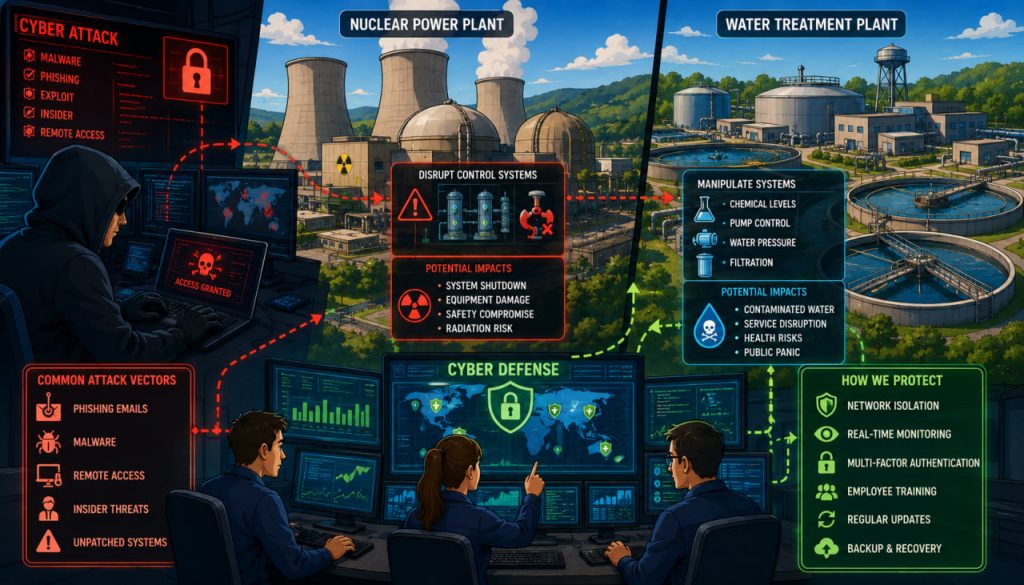
How Nuclear Facilities Can Be Targeted
Nuclear facilities use specialized industrial control systems to regulate:
- Cooling systems
- Turbines
- Sensors
- Safety mechanisms
Cyberattacks against such systems aim to:
- Disrupt operations
- Damage equipment
- Create confusion or instability
One of the most famous examples was the Stuxnet malware discovered in 2010.
Stuxnet specifically targeted Iranian nuclear centrifuges by secretly manipulating industrial control systems while hiding the damage from operators.
Cybersecurity expert Eugene Kaspersky described Stuxnet as:
“The world’s first digital weapon capable of causing physical destruction.”
The incident demonstrated that software alone could damage real industrial infrastructure.
Water Systems and Cybersecurity Risks
Water treatment plants also rely heavily on automation.
Digital systems control:
- Chemical levels
- Water pressure
- Filtration systems
- Distribution networks
Hackers targeting water systems could potentially:
- Disrupt clean water supply
- Alter chemical treatment settings
- Shut down operations
In recent years, several attempted attacks on water facilities were reported internationally, increasing concern among security experts.
Industrial Control Systems and SCADA Networks
Many critical infrastructures use systems called SCADA (Supervisory Control and Data Acquisition).
SCADA systems allow operators to monitor and control industrial equipment remotely.
These systems manage:
- Sensors
- Pumps
- Valves
- Electrical equipment
While highly efficient, connected SCADA systems also create cybersecurity challenges if improperly protected.
Why Cyberattacks Are Difficult to Stop
Cyberattacks are difficult to defend against because attackers constantly adapt.
Threats may involve:
- Malware
- Phishing emails
- Insider access
- Exploiting software vulnerabilities
Some attacks remain hidden for months before activation.
Additionally, critical infrastructure operators often prioritize operational continuity, making system upgrades slower and more complicated.
Human Error: One of the Biggest Weaknesses
Experts often emphasize that human mistakes remain one of the greatest cybersecurity risks.
Common problems include:
- Weak passwords
- Untrained employees
- Accidental malware downloads
- Poor security procedures
Even advanced security systems can fail if staff members unknowingly open dangerous files or ignore warning signs.
Cybersecurity specialist Kevin Mitnick famously said:
“The human factor is truly security’s weakest link.”
This remains highly relevant in modern cyber defense.
How Experts Protect Critical Infrastructure
Modern cyber defense uses multiple layers of protection.
Key strategies include:
- Network isolation
- Real-time monitoring
- Multi-factor authentication
- Employee cybersecurity training
- Regular software updates
- Backup systems
Some infrastructures separate critical industrial systems entirely from public internet access whenever possible.
Artificial Intelligence and Future Cyber Warfare
Artificial intelligence is increasingly influencing both cyberattacks and cybersecurity defense.
AI may help:
- Detect threats faster
- Analyze suspicious activity
- Automate security responses
However, attackers may also use AI to:
- Create more advanced malware
- Automate hacking attempts
- Generate convincing phishing attacks
This creates an ongoing technological arms race between attackers and defenders.
Why Cybersecurity Matters for Society
Modern societies depend on interconnected systems for nearly everything:
- Electricity
- Water
- Healthcare
- Transportation
- Communication
A successful cyberattack on critical infrastructure could create:
- Economic disruption
- Public panic
- Physical danger
This is why cybersecurity is increasingly treated as a national security priority worldwide.
Can Complete Protection Ever Exist?
Most experts believe no system can ever be completely invulnerable.
Instead, cybersecurity focuses on:
- Reducing vulnerabilities
- Detecting attacks quickly
- Limiting damage
- Recovering efficiently
Cybersecurity is not a one-time solution but a continuous process of adaptation.
The Future of Cyber Defense
As technology advances, cyber defense will likely become even more important.
Future protection may involve:
- AI-driven security systems
- Quantum-resistant encryption
- Autonomous monitoring networks
- More resilient infrastructure design
Governments and companies increasingly recognize that digital security is essential for modern civilization itself.
Interesting Facts
- Stuxnet was one of the first known cyber weapons designed for physical sabotage.
- Water treatment systems increasingly rely on digital automation.
- Critical infrastructure cyberattacks may remain hidden for long periods.
- Some industrial systems still operate using decades-old software.
- Cybersecurity experts often simulate attacks to test defenses.
Glossary
- Cyber Weapon — Malicious digital software or systems designed to damage or disrupt infrastructure.
- SCADA — Industrial systems used to monitor and control infrastructure remotely.
- Malware — Harmful software designed to disrupt or infiltrate systems.
- Phishing — Fraudulent attempts to steal information through deceptive communication.
- Multi-Factor Authentication — Security requiring multiple forms of identity verification.